This is a post in a series where I complete every Flare-on challenge. The landing page for all of these posts can be found here
This challenge is like a lot of the first levels is a password challenge decoding challenges. In the next screenshot, you can see what happens when you run the executable.

I opened the binary up in IDA and found the main function. The Main function starts off setting up handles to read input and loading a string from the .rdata section to a local variable.

Taking a look at the string that is loaded, it looks like to be some encoded text. I guess that it is more than likely the password.
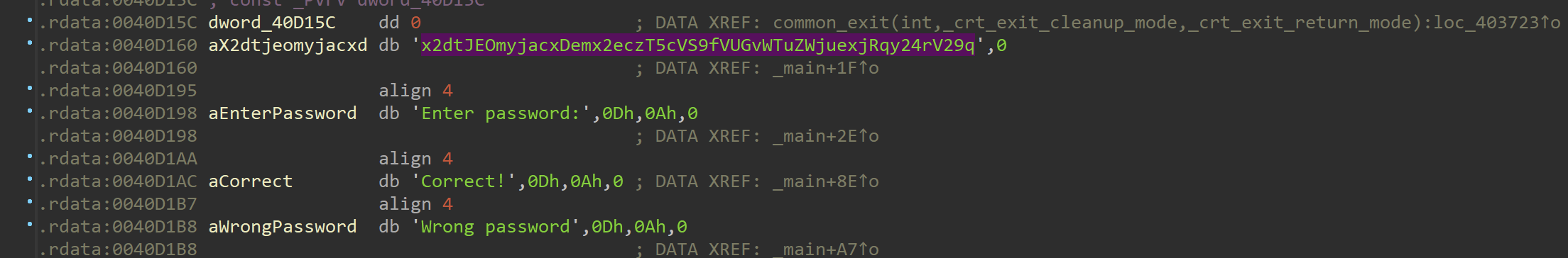
Back to the main function, after collecting the inputted password guess from the command line, it takes the inputted string and runs a function to encode it.
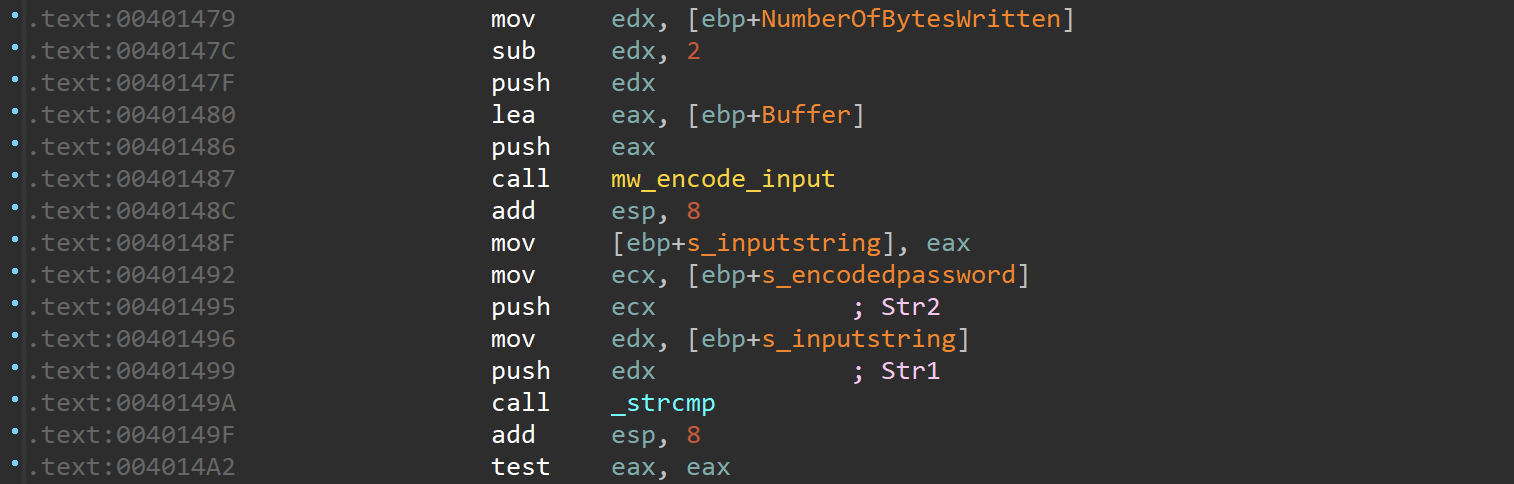
Looking at the encoder function I found what looks like a non-standard Base64 character set.

I took the custom Base64, the encoded string I found earlier, and entered them into CyberChef to decode the string. It returns what looks to be the flag.
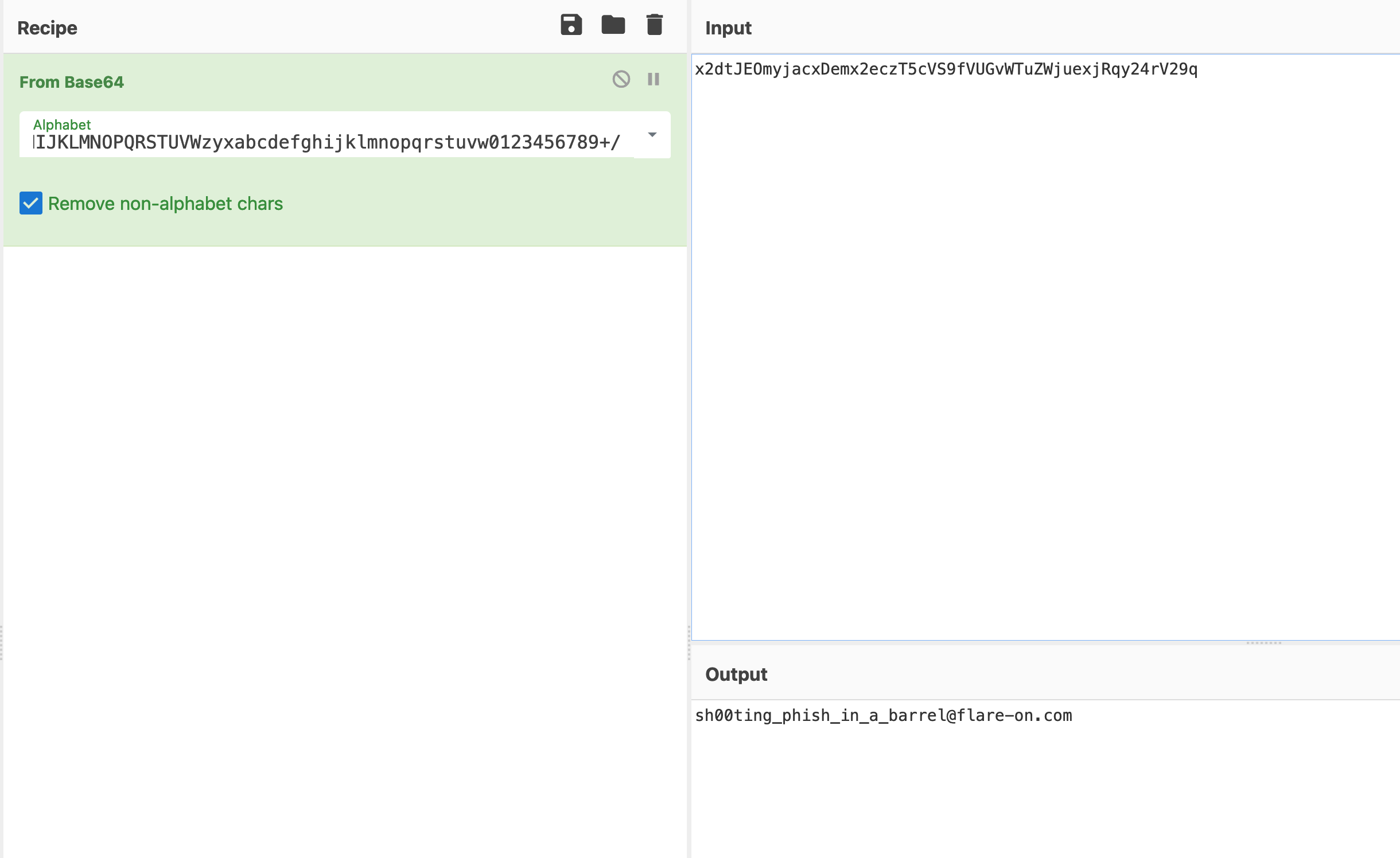
To be sure I re-ran the challenge and enter the output and bingo it validates the flag!
