This is a post in a series where I complete every Flare-on challenge. The landing page for all of these posts can be found here
In the third challenge, you are greeted with a nice goat named Elfie that when you are typing characters show up on the screen. As always I start off by checking out what kind of binary I am looking at
λ file elfie
elfie: PE32 executable (console) Intel 80386, for MS Windows
As I said we are greeted by thie goat that eats magic keys

After doing some initial analysis in Ghidra found some strings that indicate that this file might be a python executable.


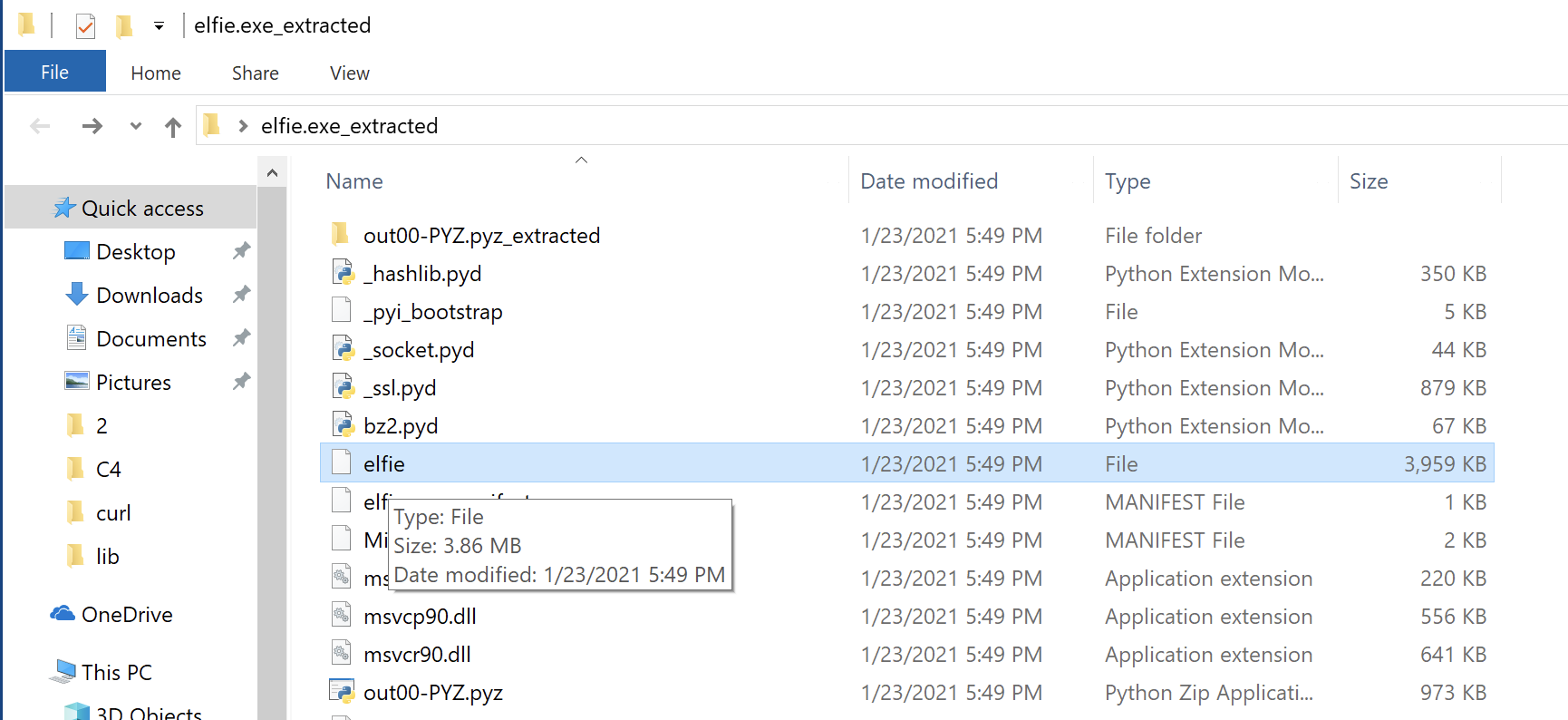
Additionally, the icon embedded in the binary should have been a giveaway. I guessed it was probably a pyInstaller executable. I ran it through pyinstextractor.py to expand it out and get a copy of the python source to analyze.
C:\Users\IEUser\Desktop
λ pyinstxtractor.py elfie.exe
C:\Tools\pyinstxtractor\pyinstxtractor.py:86: DeprecationWarning: the imp module is deprecated in favour of importlib; see the module's documentation for alternative uses
import imp
[*] Processing elfie.exe
[*] Pyinstaller version: 2.1+
[*] Python version: 27
[*] Length of package: 12034944 bytes
[*] Found 26 files in CArchive
[*] Beginning extraction...please standby
[!] Warning: The script is running in a different python version than the one used to build the executable
Run this script in Python27 to prevent extraction errors(if any) during unmarshalling
[*] Found 244 files in PYZ archive
[+] Possible entry point: _pyi_bootstrap
[+] Possible entry point: pyi_carchive
[+] Possible entry point: elfie
[*] Successfully extracted pyinstaller archive: elfie.exe
You can now use a python decompiler on the pyc files within the extracted directory
C:\Users\IEUser\Desktop
I found the file elfie and opened it in VSCode to look at the contents.
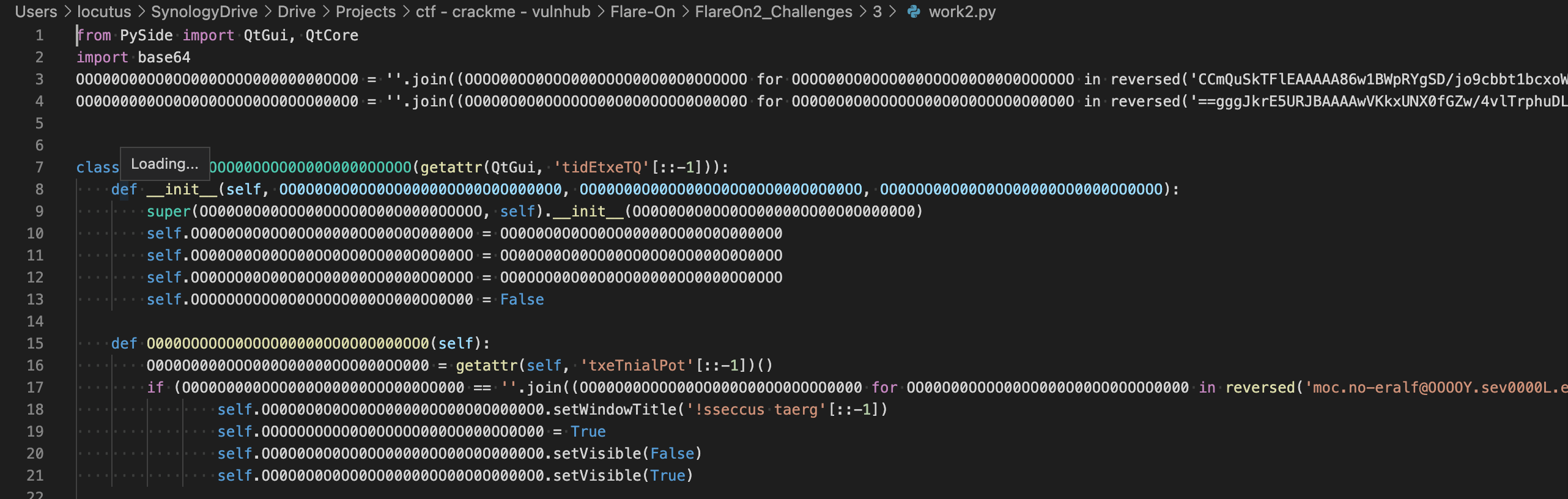
it looks to be full of Base64 strings that are concatenated together, decoded, and executed.

I changed the final operation to print the encoded python code for further analysis.

The next layer down looked more like normal python code with obfuscated variable names.
Even looking at the obfuscated code the is pretty obvious but I wanted to clean up some of the variable names to make sure I was not missing anything else.
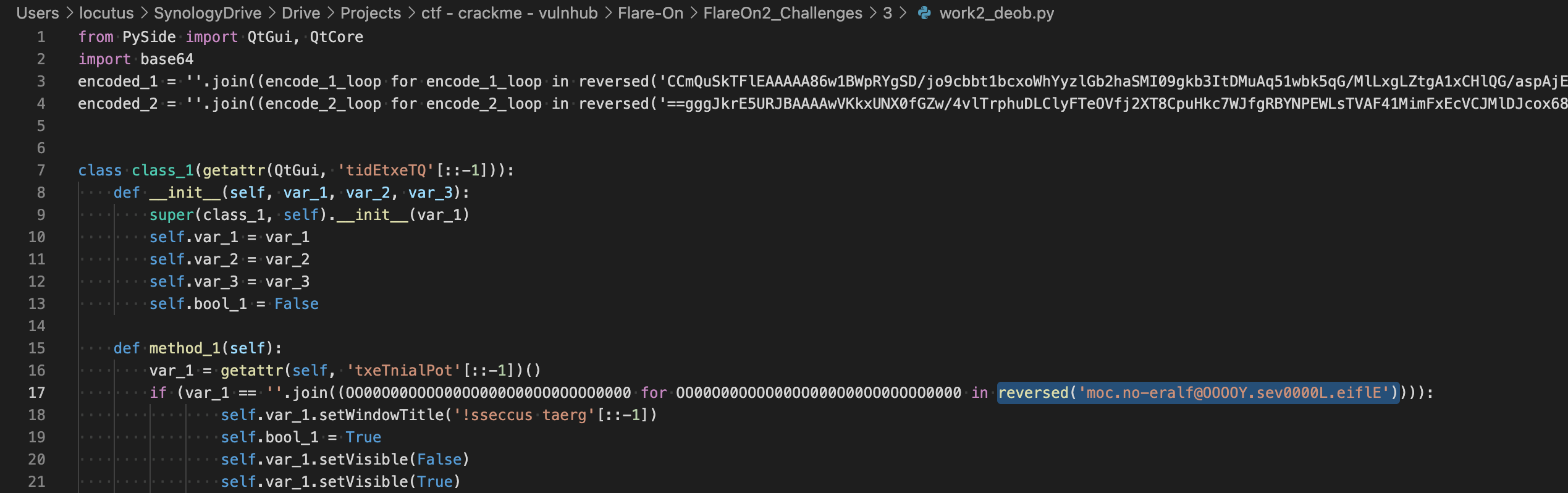
After reversing the string the flag is revealed

and Elfie is happy!
