This is a post in a series where I complete every Flare-on challenge. The landing page for all of these posts can be found here
This challenge includes two files, a packet capture formatted in PCAP format and a Windows binary.

Opening up the PCAP in Wireshark, I found multiple HTTP streams submitting POST requests. I looked at each of these POST requests and saw they all have a few bytes of content.
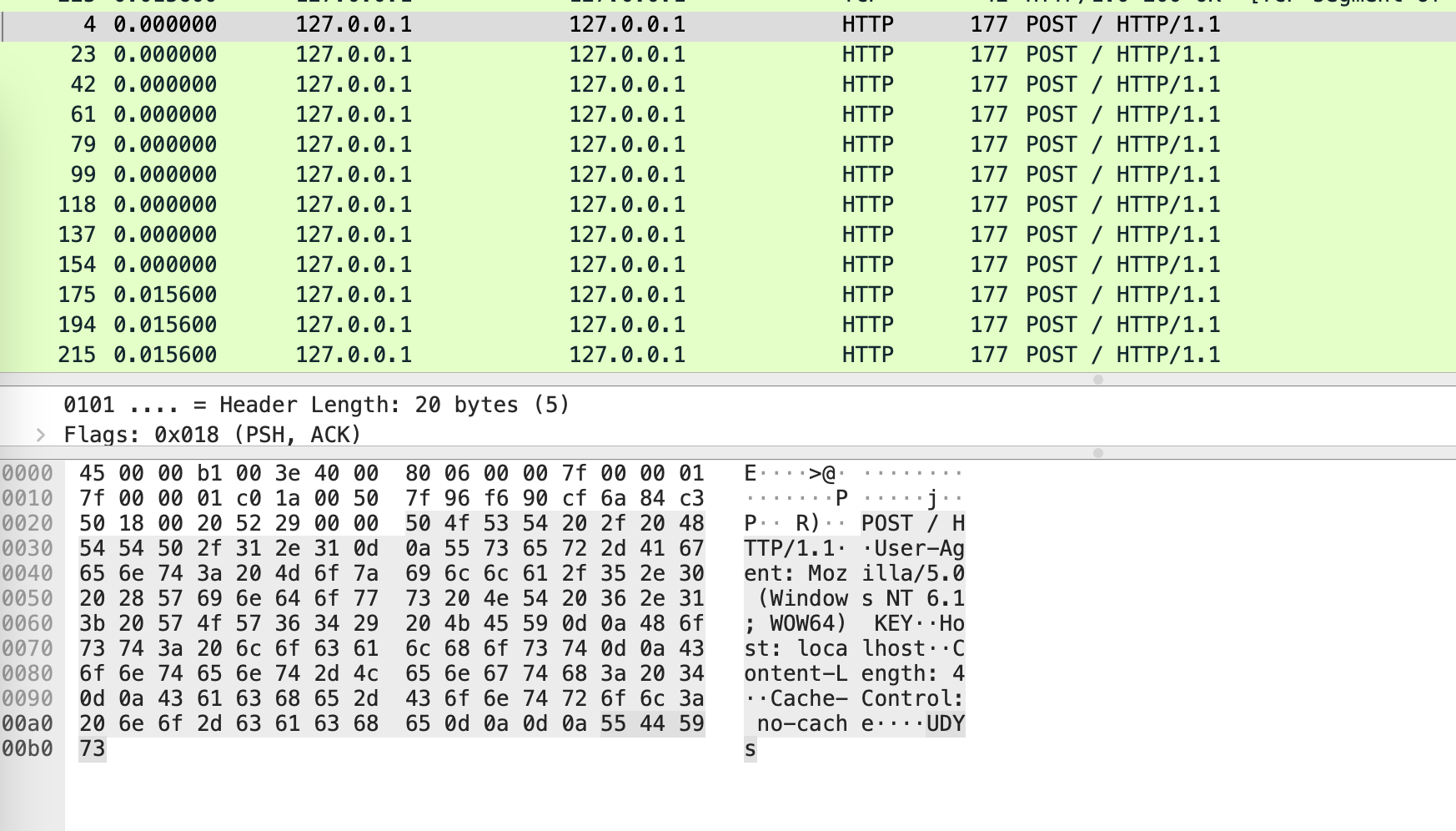
I copied the data from each of these HTTP POST requests and found what looked like a Base64 encoded string.
UDYs1D7bNmdE1o3g5ms1V6RrYCVvODJF1DqxKTxAJ9xuZW=
When I attempted to decode it using standard Base64 character sets I did not find any recognizable data. I knew that it wouldn’t be that easy.
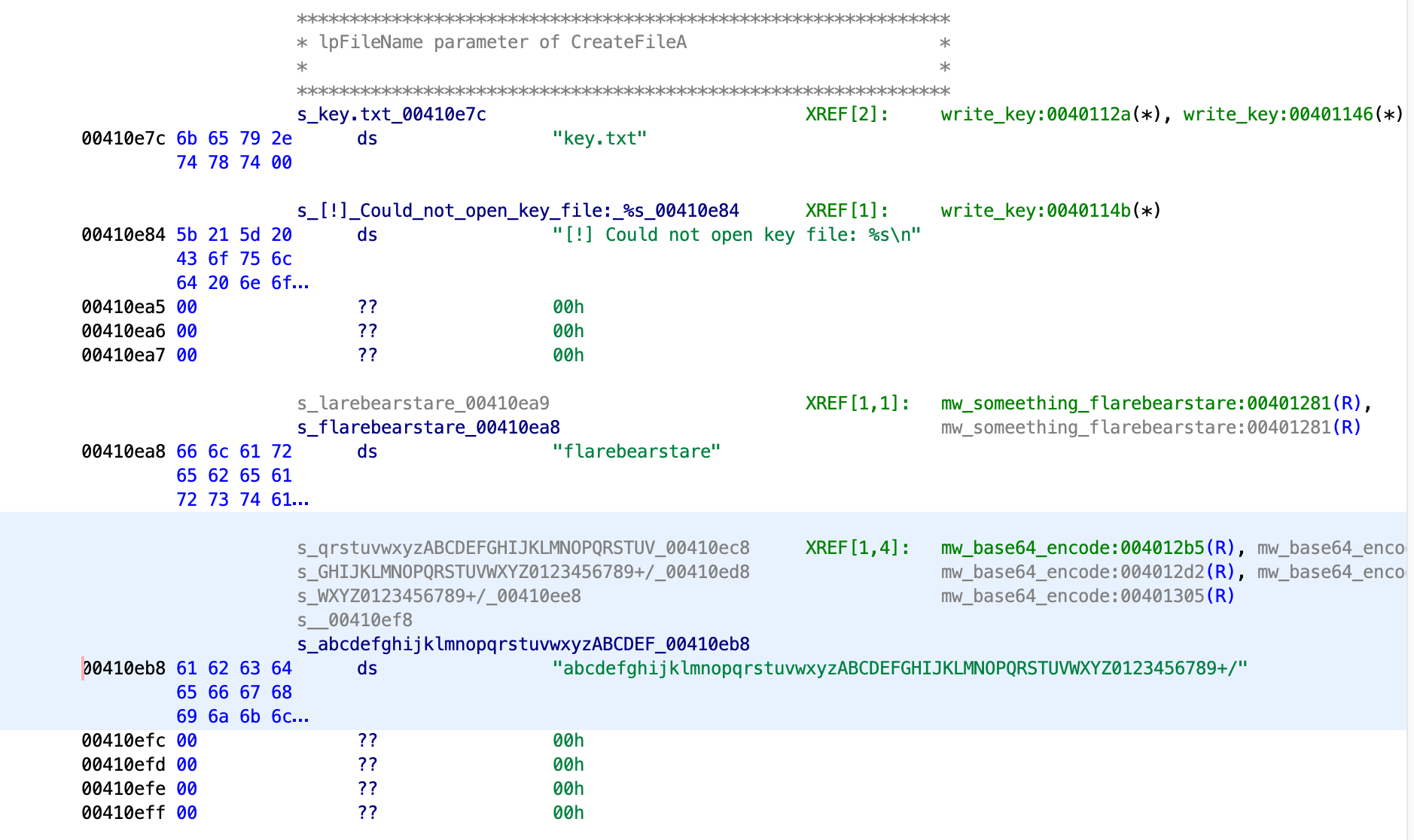
Looking at the strings in the binary, I found two interesting strings, “flarebearstare” which could be a password, and another string that looks like a Base64 alphabet with the uppercase and lower case sections swapped in order.
I following the cross-reference for the “flarebearstare” string, finding a function with a data decoder loop. This function is passed data and loops through each byte, subtracting each character in order of “flarebearstare” from the current byte.

Looking over this functionality, I started to write up some code to decode the flag. I grabbed a Base64 library that needed a small modification to use a custom character set. My fork of the code can be found at this repo.
https://github.com/suidroot/Python-Base64
In the screenshot below, you can see my final script in a Jupyter notebook. As an aside, I have been using it for many challenges and other projects to test out decoder and other functionality. They have been instrumental in quick prototyping and experimentation.
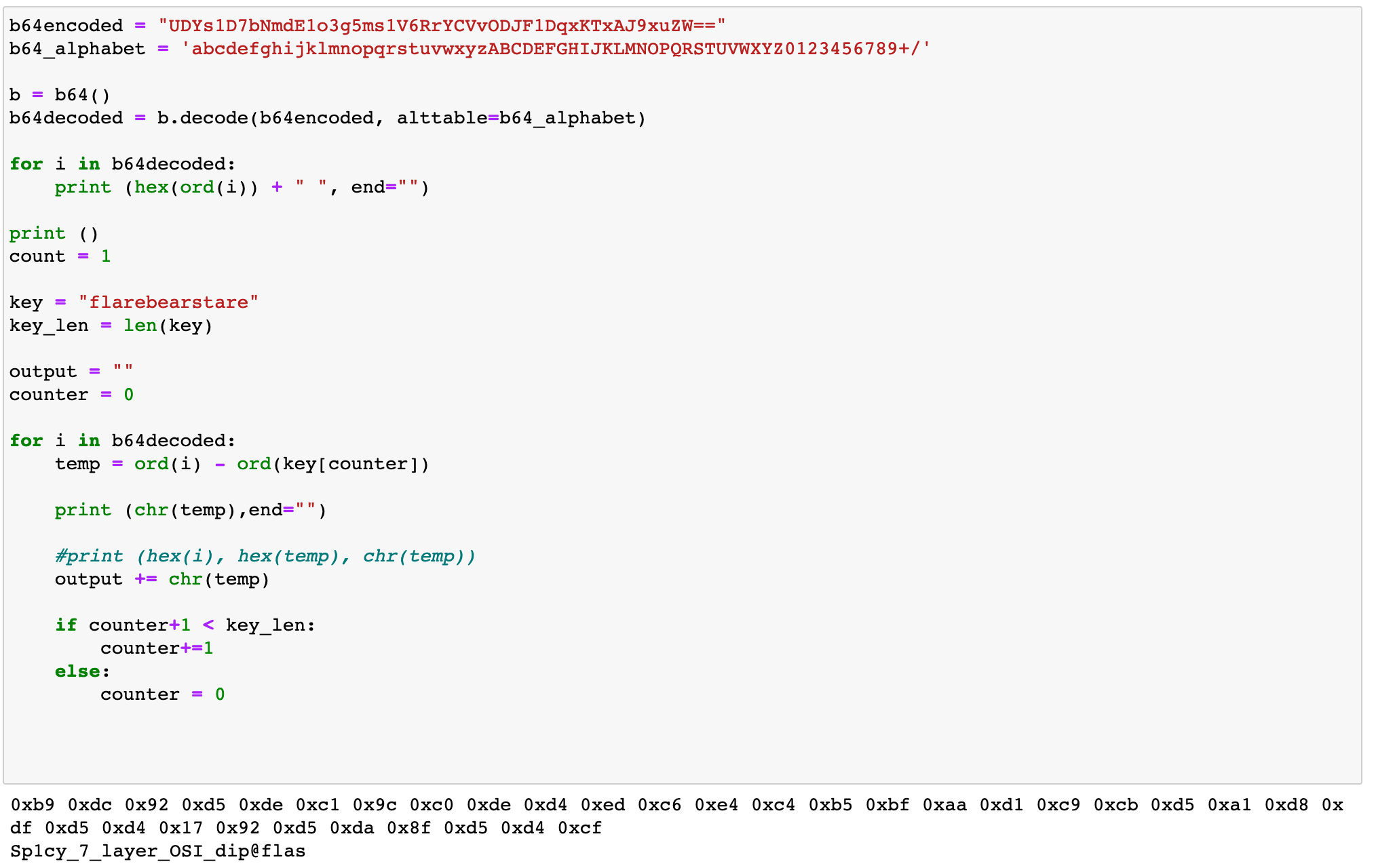
Success there mostly is the flag. You can see there is some weirdness in the decoding of the flag, but this script decodes the main part of it needed in my mind to call it a solution.
Full Code
b64encoded = "UDYs1D7bNmdE1o3g5ms1V6RrYCVvODJF1DqxKTxAJ9xuZW=="
b64_alphabet = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789+/'
b = b64()
b64decoded = b.decode(b64encoded, alttable=b64_alphabet)
for i in b64decoded:
print (hex(ord(i)) + " ", end="")
print ()
count = 1
key = "flarebearstare"
key_len = len(key)
output = ""
counter = 0
for i in b64decoded:
temp = ord(i) - ord(key[counter])
print (chr(temp),end="")
#print (i, hex(temp), key[counter], chr(temp))
output += chr(temp)
if counter+1 < key_len:
counter+=1
else:
counter = 0