This is a post in a series where I complete every Flare-on challenge. The landing page for all of these posts can be found here
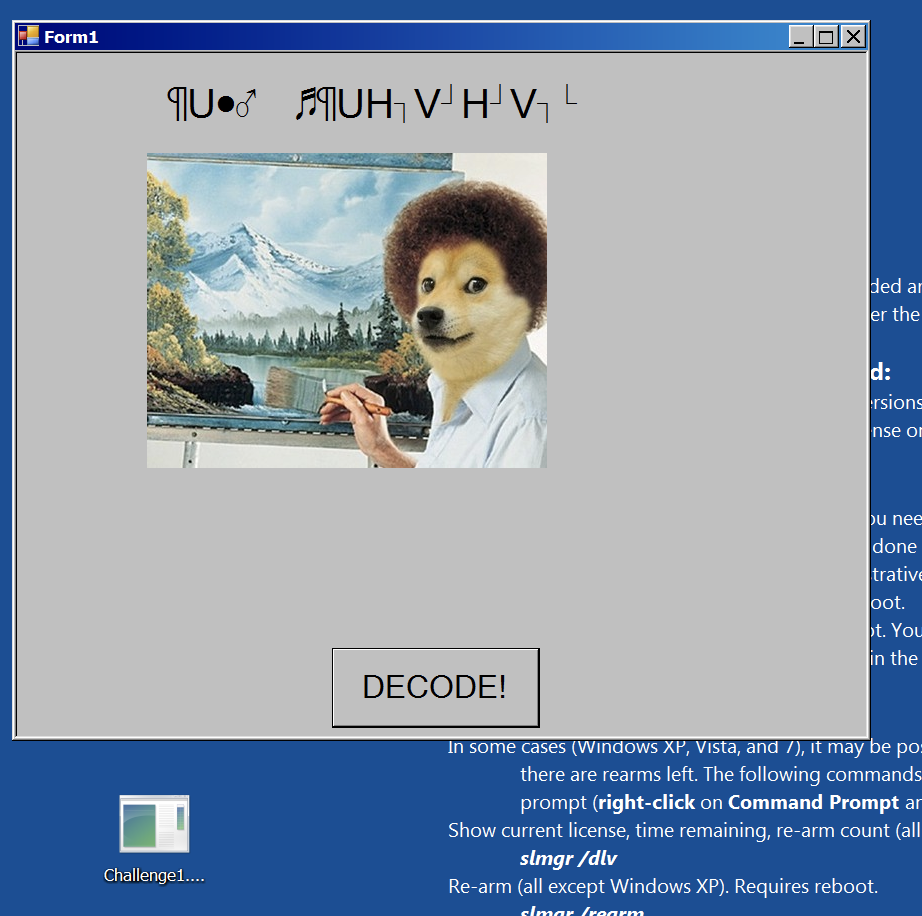
In the very first challenge you are presented with a windows executable and when you run it you are presented with a Bob Ross painting a nice scene.

But, when you click DECODE! You get a Bob Doge with an weird text string.
Digging a little deeper to see what type of file we have we find we hace a .NET executable.
$ file Challenge1.exe
Challenge1.exe: PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows
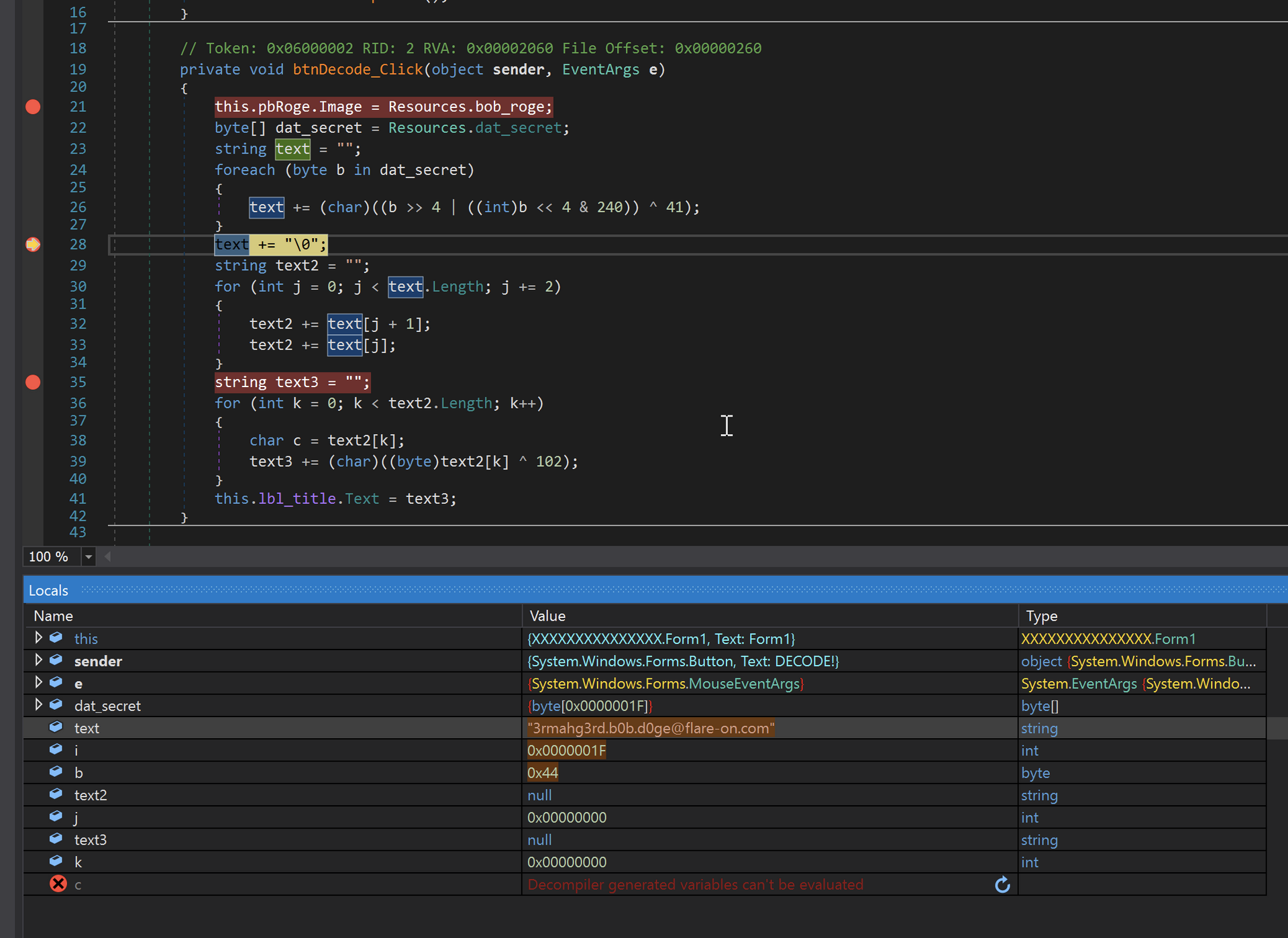
I next loaded the file up in dnSpy and after navigating from the entry point into Form1. I found the following code block.
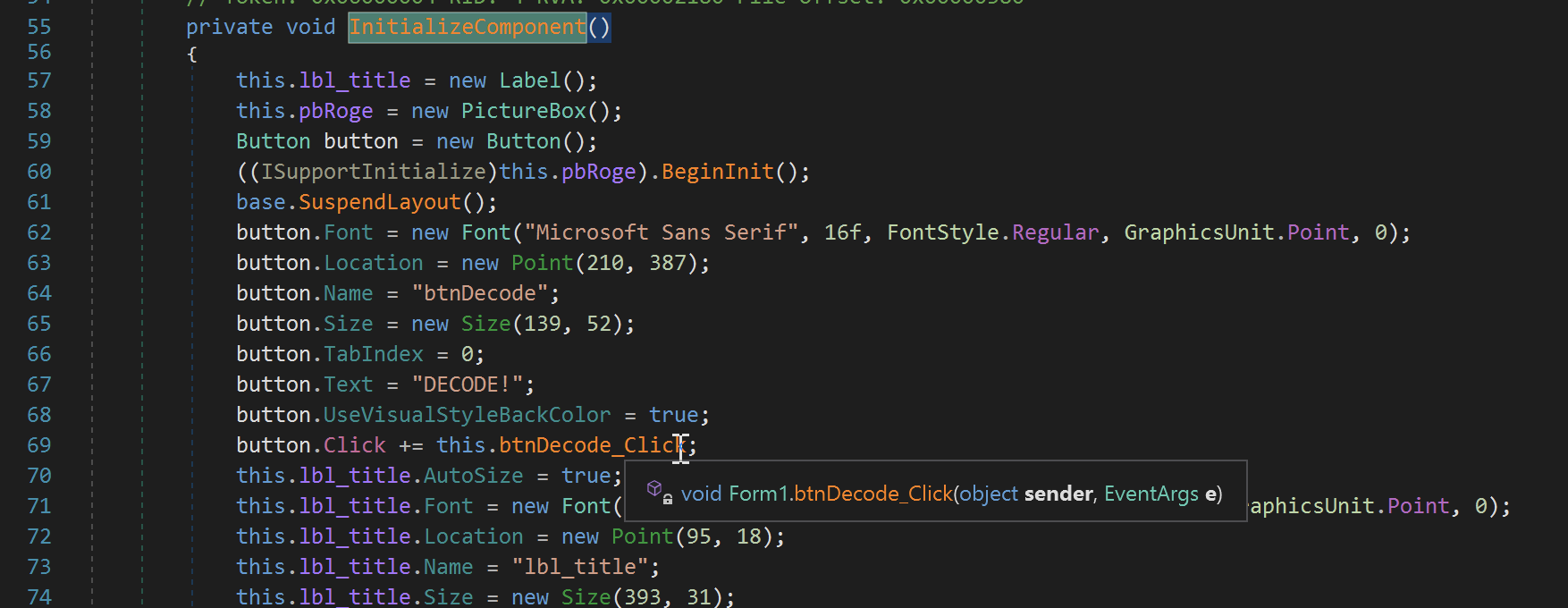
The function “btnDecode_Click()” looks very interesting, when stepping into it I find what looks to be a decoding algorithm that pulls its content from the Resources. I set a few breakpoints on the code just after the loops.
After running to the breakpoint after the first loop the flag is in clear text in the “text” variable. The next few loops re-encode the flag to return an obscured output shown in the UI.